Ari Juels
Weill Family Foundation and Joan and Sanford I. Weill Professor
Jacobs Technion-Cornell Institute
Cornell Tech
2 West Loop Road
New York, NY 10044
e-mail:![]()
The Oracle 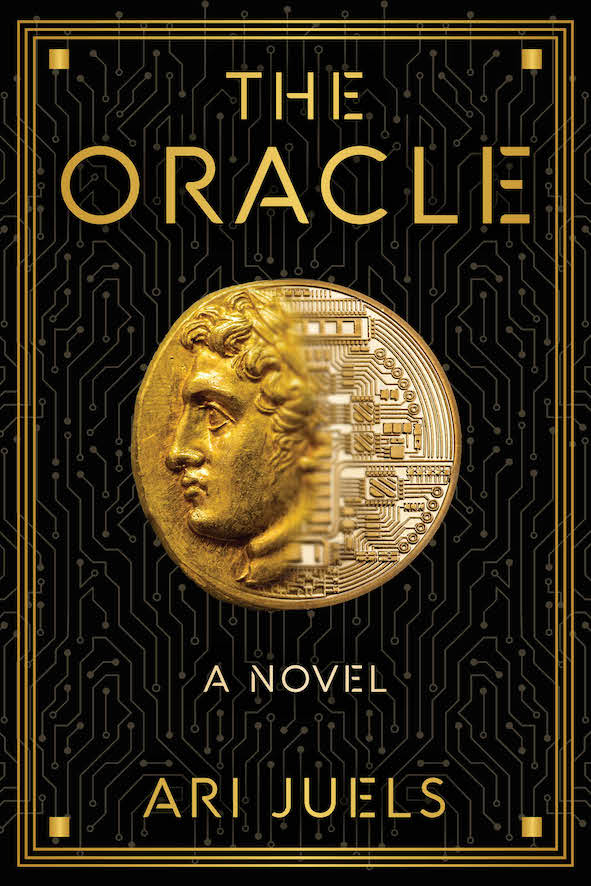
My crypto thriller novel The Oracle was released on 20 February 2024 (by Talos Press). To learn about it, visit the book website: www.oraclenovel.com.
Bio
Ari Juels is the Weill Family Foundation and Joan and Sanford I. Weill Professor in the Jacobs Technion-Cornell Institute at Cornell Tech and the Technion and a Computer Science faculty member at Cornell University. He is a Co-Director of the Initiative for CryptoCurrencies and Contracts (IC3). He is also Chief Scientist at Chainlink Labs.
He is the author of crypto thriller novel The Oracle (Talos Press).
He was the Chief Scientist of RSA, Director of RSA Laboratories, and a Distinguished Engineer at EMC (now Dell EMC), where he worked until 2013. He received his Ph.D. in computer science from U.C. Berkeley.
His recent areas of interest include blockchains, cryptocurrency, and smart contracts, as well as applied cryptography, user authentication, and privacy.
Group members
PhD Students:
-
- James Austgen
- Kushal Babel
- Yan Ji
- Mahimna Kelkar
Visiting Scientist:
Group Alumns
-
- Deepak Maram, PhD, 2023 -> Mysten Labs
- Ethan Cecchetti (Co-advised with Andrew Myers), PhD, 2021 -> Univ. of Wisconsin
- Phil Daian -> Flashbots
- Fan Zhang, PhD, 2020 -> Yale University
- Sishan Long, MS, 2023 -> Espresso Systems
Postdocs:
-
- Sam Scott (Co-mentored with Tom Ristenpart, Runway program) -> Oso (Co-founder)
- Ian Miers (Co-mentored with Tom Ristenpart) -> UMD
- Steven Goldfeder (Co-mentored with Andrew Miller) -> Arbitrum (CEO)
Prospective Ph.D. students
In general, Cornell / Tech is an exceptional place to do research on the science of blockchains, as well as security, privacy, and crypto. Note that Cornell’s computer science program spans the Ithaca and NYC campuses; students reside in whichever location their advisor does.
In order to work with me or any other faculty member in the Cornell CS as a Ph.D. student, however, you must first be accepted by the Cornell CS program. Individual faculty members cannot admit students, and Cornell CS encourages students to explore working with different potential advisors. If you believe you may wish work with me, please list me as a contact in your application to the Ph.D. program.